Are you concerned about sensitive data leaving your office? You should be.
Unfortunately, too many business owners assume that their in-house security measures are adequate. The truth is that traditional in-house computer systems are vulnerable to abuse, yet the inherent risks aren’t always obvious.
With VCIT Cloud Apps and Desktops, you don’t need to deal with the complexities and headaches of securing your sensitive data.
Here’s why…
In contrast, a typical small business computer system is vulnerable to theft, fire, flood and other risks that can cripple your business and have devastating consequences.![]()
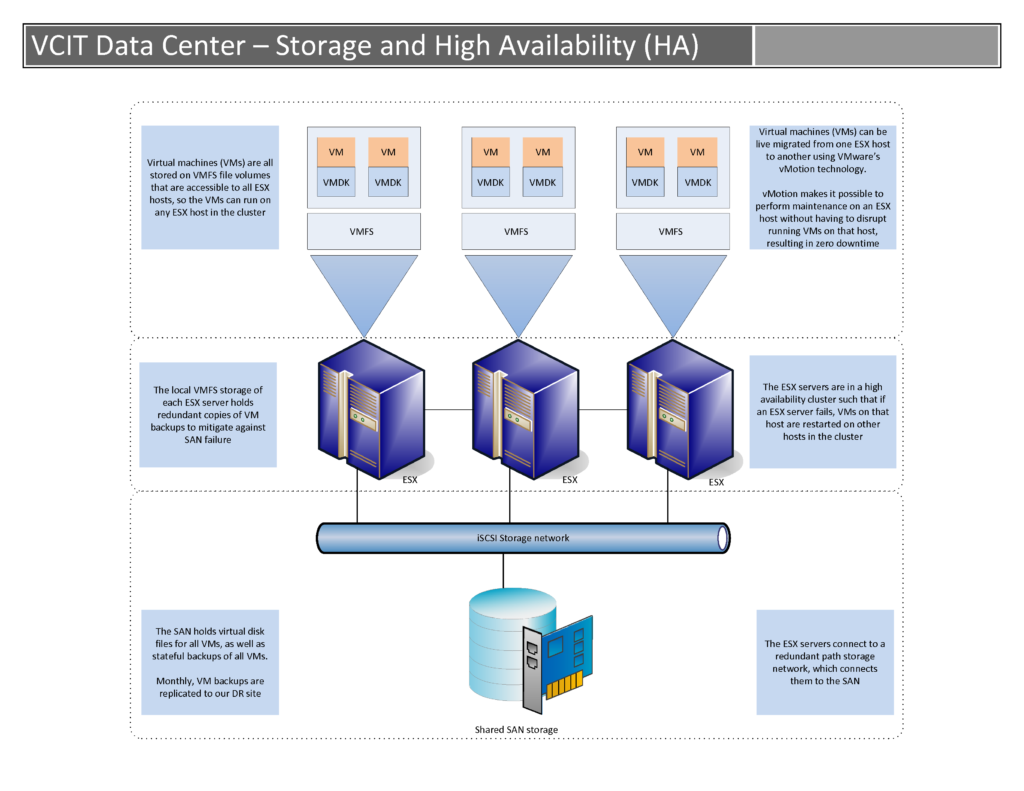
Also, our comprehensive backup systems ensure that your data is always backed up, giving you peace of mind should disaster strike. We take snapshots of your documents multiple times a day, perform nightly differential backups, weekly full backups, monthly offsite encrypted backups, and replicate those backups to our DR site too.![]()
In contrast, our enterprise class firewall systems allow your staff to safely connect to resources over the Internet while mitigating the risk of attack.![]()
Key security benefits of hosting with VCIT
Clearly, getting your valuable information off of portable device hard drives should be a top priority. VCIT Cloud Apps and Desktops solves this problem by centralizing all of your company data in a high security data center.![]()
With a typical retail firewall appliance, an attacker could repeatedly connect to the server and either crash it (denial of service attack) or run a password guessing program against it. In either case, a cheap retail firewall would neither detect nor prevent the attack.![]()
How quickly can you restore all of your critical data?
Statistics show that a majority of businesses that experience a major data loss go out of business within a year of the incident.![]()
On your firewall too?